APT28 exploited CVE-2026-21509 within three days of patch disclosure. This isn’t a bug report. It’s a systemic market failure.
THE TIMELINE THAT SHOULD SHAKE YOU
January 26, 2026. Microsoft releases an out-of-band patch for CVE-2026-21509—a security feature bypass vulnerability in the world’s most ubiquitous productivity suite.
January 29, 2026. Malicious documents exploiting that exact flaw begin circulating in Ukraine .
Seventy-two hours. That’s how long it took Russia’s GRU military intelligence unit—APT28, Fancy Bear, Forest Blizzard—to weaponize a vulnerability, craft phishing lures, and deploy MiniDoor and PixyNetLoader malware into Ukrainian systems .
This isn’t a story about patch latency. It’s a story about structural collapse.
THE NEW ATTACK VELOCITY
We have entered an era where threat actors operate at machine speed while defenders still operate on human time.
The Check Point Research January 2026 Threat Report confirms what we already fear: global organizations now face an average of 2,090 attacks per week—a 17% year-over-year increase . Ransomware attacks have surged 10% in a single month, led by Qilin, LockBit, and Akira .
But numbers don’t capture the qualitative shift. What’s changed isn’t volume. It’s intent.
APT28 wasn’t opportunistically scanning for unpatched systems. They were waiting. They had the weapon pre-loaded. The moment Microsoft disclosed the flaw, the trigger was pulled .
THE MICROSOFT MONOCULTURE: A NATIONAL SECURITY LIABILITY
Here’s the uncomfortable truth no one wants to say aloud:
We built the digital infrastructure of Western governments, critical infrastructure, and global enterprises on a single vendor’s foundation. And that foundation now has a structural crack that sophisticated adversaries are exploiting with surgical precision.
As former UK Cabinet Office director Bill McCluggage writes, this isn’t a cyber security challenge—it’s a market structure problem .
When one company controls the productivity suite used by practically every government and enterprise globally, vulnerabilities don’t fail in isolation. They cascade.
Recent Azure outages demonstrated how a single point of failure in Redmond can ripple across continents. Now we’re watching Russian military hackers weaponize Office documents as standard-issue warfare tools .
This is aggregation risk on a geopolitical scale.
THE AI PARADOX: YOUR EMPLOYEES ARE THE NEW BATTLEFIELD
Simultaneously, a parallel crisis is unfolding.
The Check Point report reveals a staggering statistic: 93% of organizations using GenAI tools have experienced serious sensitive data exposure through employee prompts . One in every 30 corporate GenAI queries contains confidential information—source code, PII, customer data, internal strategy documents .
Enterprises now average 10 different GenAI tools in active use, most outside formal IT governance .
We are fighting state-sponsored malware with one hand while our employees voluntarily feed proprietary data into unsecured third-party AI models with the other.
THE GLOBAL TARGET MAP: WHO’S UNDER ATTACK RIGHT NOW
While APT28 hunts in Ukraine, other fronts are burning:
THE NORTH KOREAN AI ESCALATION
Let’s pause on that last line.
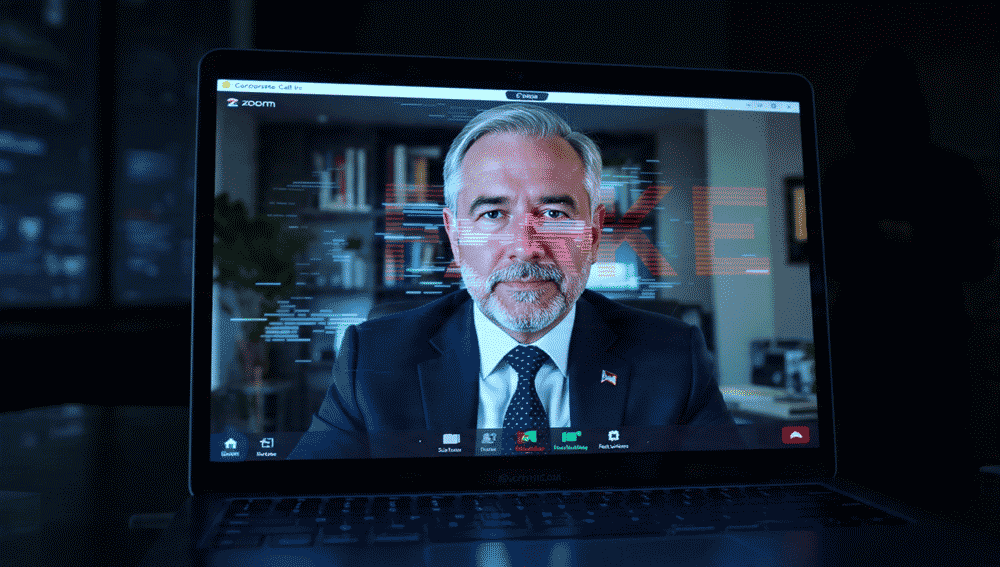
North Korea’s UNC1069—also tracked as MASAN or CryptoCore—didn’t just send phishing emails. They hijacked a Telegram account, scheduled a fake Zoom meeting, and deployed a deepfake video of a real cryptocurrency executive to convince their target to execute malicious commands .
This is no longer theoretical. AI-generated identity fraud is here, it’s operational, and it’s defeating human judgment.
WHAT CISOS MUST DO NOW: THE RESILIENCE IMPERATIVE
The era of “prevention alone” is over. Here is your February 2026 action checklist:
1. Assume Microsoft Office Is Compromised
Treat Office documents from unknown senders as potential malware vectors. Deploy behavioral detection tools that don’t rely on signature matching. CVE-2026-21509 is patched—but the next one is already being weaponized .
2. Audit Your GenAI Shadow IT
You cannot secure what you cannot see. Inventory every AI tool your employees use. Block unsanctioned platforms. Deploy DLP controls specifically for GenAI prompt submission .
3. Patch With Zero Trust
Automated patch deployment is no longer optional. If your organization relies on manual patching schedules or bandwidth-constrained remote sites, you are a shooting gallery .
4. Test Deepfake Defenses
Your executive team needs training—not on spotting typos, but on detecting synthetic media. Establish verbal challenge codes for financial transactions and sensitive communications .
5. Demand Vendor Accountability
CISOs must begin asking vendors: What is your weaponization window? How quickly are adversaries exploiting your disclosures? Procurement decisions should incorporate exploit velocity metrics .
6. Plan for Systemic Collapse
What happens if Microsoft experiences a weeks-long global outage? If Azure goes dark? If Office activation servers are compromised? Run the exercise. Document the answer .
CONCLUSION: THE MONOCULTURE MUST END
The 72-hour weaponization of CVE-2026-21509 is a warning, not a verdict.
Regulators are beginning to recognize that market concentration equals national security vulnerability. The UK Competition and Markets Authority and European Commission’s Directorate-General for Competition have roles to play .
But you cannot wait for structural remedies that take years. Your network is under attack today.
The adversary has AI. They have automation. They have patience and state sponsorship.
What they don’t have is your ability to adapt, diversify, and refuse to accept monoculture as destiny.
The question is no longer whether Microsoft is secure. It’s whether we can survive our dependence on them.
APT28, #MicrosoftOffice, #CVE202621509, #ZeroDay, #CyberAttack2026, #GenAISecurity, #DeepfakeThreat, #SupplyChainAttack, #PatchTuesday, #TelecomBreach, #UNC3886, #OperationCyberGuardian, #Ransomware, #CISO, #DigitalMonoculture