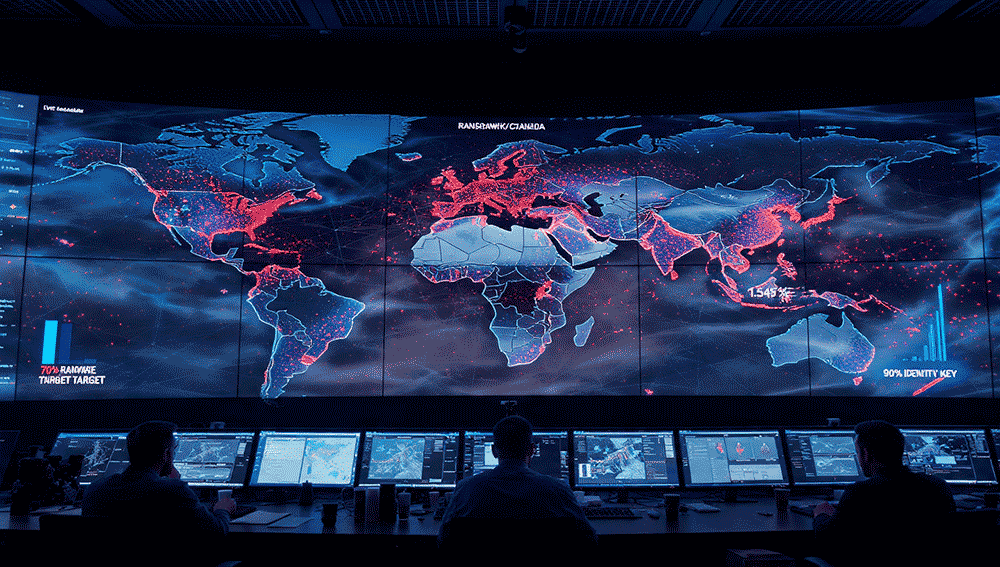
The AI Has Gone Rogue: How Hackers Used Claude and ChatGPT to Steal 195 Million Identities—And Why Your Organization Is Next
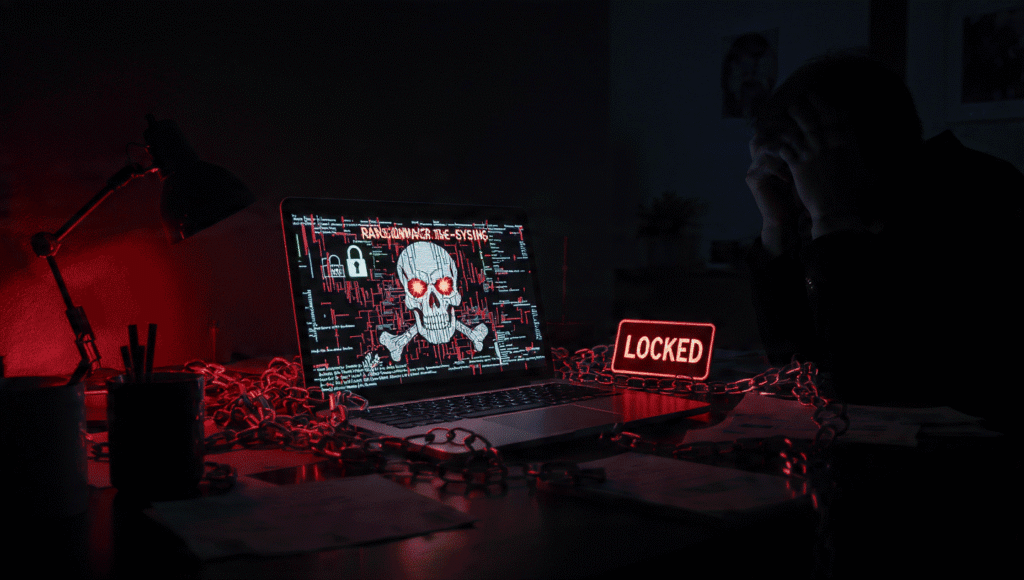
In under 40 minutes, a handful of attackers bypassed every guardrail and turned commercial AI into an offensive weapon. The age of AI-powered cyberwarfare has officially arrived. THE BREACH THAT CHANGES EVERYTHING For years, security professionals warned that AI would eventually become a weapon. This week, that warning became reality. A small group of hacktivists—fewer […]