New data reveals a tsunami of never-before-seen malware, 96% encrypted delivery, and an identity crisis driving 90% of breaches. The old security playbook is obsolete.
THE NUMBERS THAT SHOULD STOP YOU COLD
Let’s start with three statistics that define February 20, 2026:
1,548%. That’s the spike in new, unique malware from Q3 to Q4 2025—a single-quarter explosion of never-before-seen threats .
96%. The percentage of malware now delivered over encrypted TLS connections, invisible to organizations without HTTPS inspection .
90%. The share of breaches where identity weaknesses played a material role .
These aren’t incremental changes. They represent a fundamental reset of the threat landscape. And they arrived in the same 48-hour window.
THE MALWARE TSUNAMI: WHY QUARTERLY SPIKES NOW MEASURE IN THOUSANDS OF PERCENT
WatchGuard’s latest Internet Security Report reveals a terrifying acceleration: new malware increased every quarter throughout 2025, culminating in a 1,548% Q4 spike .
But volume is only half the story.
Twenty-three percent of detected malware evaded traditional signature-based detection entirely—effectively qualifying as zero-day threats . These aren’t variants of known families. They’re novel code, purpose-built to bypass yesterday’s defenses.
The implications are stark: organizations relying on signature matching are now flying blind against nearly a quarter of incoming threats.
THE ENCRYPTION PARADOX: YOUR SECURITY TOOLS CAN’T SEE WHAT THEY CAN’T SCAN
Here’s the cruel irony of modern network defense: the same encryption that protects your data now protects your attackers.
With 96% of blocked malware delivered over TLS, organizations without HTTPS inspection face a massive visibility gap . Malware flows through encrypted channels, indistinguishable from legitimate traffic until it’s too late.
This isn’t a technical limitation—it’s an architectural blindspot baked into networks that treat encryption as an endpoint-only problem.
THE IDENTITY CRISIS: 90% OF BREACHES START WITH “LOG IN,” NOT “BREAK IN”
Unit 42’s Global Incident Response Report 2026 delivers a sobering finding: identity weaknesses played a role in nearly 90% of investigations .
Attackers increasingly don’t “break in”—they “log in” using stolen credentials and tokens . They exploit fragmented identity estates, escalate privileges, and move laterally as authorized users.
This explains why MFA bypass kits like “Starkiller” are thriving on dark web marketplaces . When identity is the perimeter, compromising identity means compromising everything.
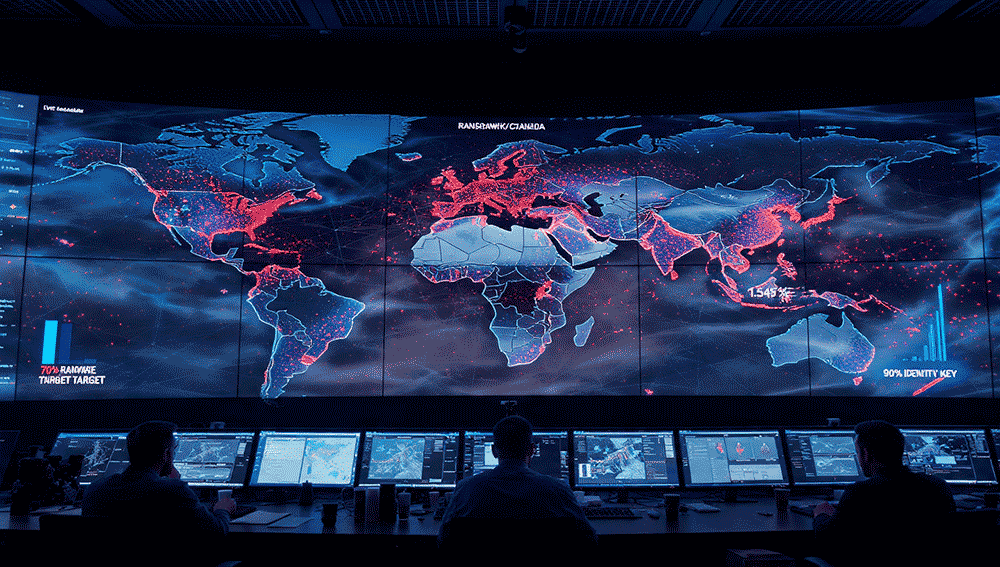
THE GEOPOLITICAL TARGET MAP: WHO’S IN THE CROSSHAIRS
Nozomi Networks’ OT & IoT Security Report reveals a concentrated targeting pattern: 70% of global ransomware activity focuses on English-speaking countries .
- United States: 40% of all ransomware attacks
- Canada + United Kingdom: Combined 30% of attacks
These three nations represent nearly 30% of world GDP . Attackers aren’t just after data—they’re pursuing macroeconomic disruption.
Scattered Spider alone accounted for 42.9% of all actor-related alerts, followed by Kimsuky (North Korea), APT29 (Russia), CURIUM (Iran), and Mustard Tempest .
ACTIVE ZERO-DAYS: WHAT’S BEING EXPLOITED RIGHT NOW
CISA added multiple vulnerabilities to its Known Exploited Vulnerabilities catalog this week, confirming active exploitation :
The diversity is staggering—from brand-new Chrome zero-days to nearly two-decade-old Microsoft flaws. Attackers are pragmatic, not fashionable .
THE AI ACCELERATION: COMPRESSING THE ATTACK LIFECYCLE
Unit 42’s report identifies AI as a force multiplier for threat actors, compressing the attack lifecycle from access to impact . In 2025, exfiltration speeds for the fastest attacks quadrupled.
Nation-state actors increasingly rely on persona-driven infiltration—fake employment, synthetic identities—and deeper compromise of core infrastructure .
The World Economic Forum’s Global Cybersecurity Outlook 2026 confirms this acceleration: 87% of leaders see AI-related vulnerabilities as the fastest-growing cyber risk .
THE SUPPLY CHAIN SHIFT: BEYOND VULNERABLE CODE
Software supply chain risk has evolved. Attackers now exploit SaaS integrations, vendor tools, and application dependencies to bypass perimeters at scale .
Recent examples include:
- Notepad++ update mechanism hijacked by China-linked actors to selectively distribute malware
- OpenClaw AI agent framework targeted by infostealer malware for sensitive configuration data
- “AI as a C2 proxy” technique using Microsoft Copilot and Grok as covert command-and-control relays
THE WIRELESS WEAKNESS: CRITICAL INFRASTRUCTURE’S SOFT UNDERBELLY
Nozomi’s report exposes dangerous wireless security gaps in industrial environments :
- 68% of wireless networks operate without Management Frame Protection despite modern encryption
- 98% rely on Pre-Shared Key authentication—acceptable for coffee shops, catastrophic for industrial enterprises
- Only 2% use enterprise-grade authentication (802.1X)
Shared credentials remove accountability and enable long-term reuse. Once exposed, legitimate access becomes indistinguishable from misuse.
WHAT CISOS MUST DO NOW: THE FEBRUARY 2026 PLAYBOOK
1. Assume Encrypted Traffic Is Malicious Until Proven Otherwise
With 96% of malware delivered over TLS, HTTPS inspection is no longer optional . You cannot defend what you cannot see.
2. Treat Identity as the New Perimeter
MFA is baseline. Privileged access management is mandatory. Assume credentials are compromised and monitor for anomalous behavior .
3. Deploy Behavioral, AI-Driven Detection
With 23% of malware evading signatures, behavioral detection is essential . Signature matching alone guarantees eventual breach.
4. Patch With Zero Trust—And Zero Delay
CISA’s KEV catalog additions demand immediate action . Quarterly patching is now a liability. Automate critical updates.
5. Audit Wireless Networks Immediately
If your industrial environments rely on PSK authentication, assume compromise . Migrate to 802.1X and enforce Management Frame Protection.
6. Map Your Identity Estate
You cannot secure what you cannot inventory. Map every identity, every permission, every token .
7. Prepare for “Harvest Now, Decrypt Later”
Australia’s ACSC warns that adversaries collect encrypted data today for quantum decryption tomorrow . Start quantum-resistant migration planning.
CONCLUSION: THE BASELINE JUST SHIFTED
The 1,548% malware spike isn’t an anomaly. It’s the new baseline.
When 96% of threats arrive encrypted, 23% evade signatures, and 90% of breaches exploit identity, the old playbook isn’t just outdated—it’s dangerous.
Attackers operate at machine speed with AI acceleration. They target English-speaking economies for macroeconomic disruption. They exploit wireless weaknesses, SaaS integrations, and vendor tools.
The question facing every CISO today:
Are your defenses built for 2023’s threats—or 2026’s?
The data says the gap is widening. The response starts now.
MalwareSpike2026, #1548Percent, #EncryptedThreats, #IdentityCrisis, #ZeroTrustNow, #CISAKEV, #CVE20262441, #CVE202622769, #RansomwareTargets, #ScatteredSpider, #APT29, #Unit42, #WatchGuard, #NozomiNetworks, #OTSecurity, #WirelessVulnerability, SupplyChainAttack, #AIacceleration, #CyberResilience, #PatchTuesday